Home>Technology and Computers>Introducing FTP And FTPS Support For AWS Transfer
Technology and Computers
Introducing FTP And FTPS Support For AWS Transfer
Modified: February 29, 2024
Introducing FTP and FTPS support for AWS Transfer. Enhance your technology and computer systems with secure file transfer protocols. Discover the benefits today!
(Many of the links in this article redirect to a specific reviewed product. Your purchase of these products through affiliate links helps to generate commission for Noodls.com, at no extra cost. Learn more)
Table of Contents
Overview of AWS Transfer
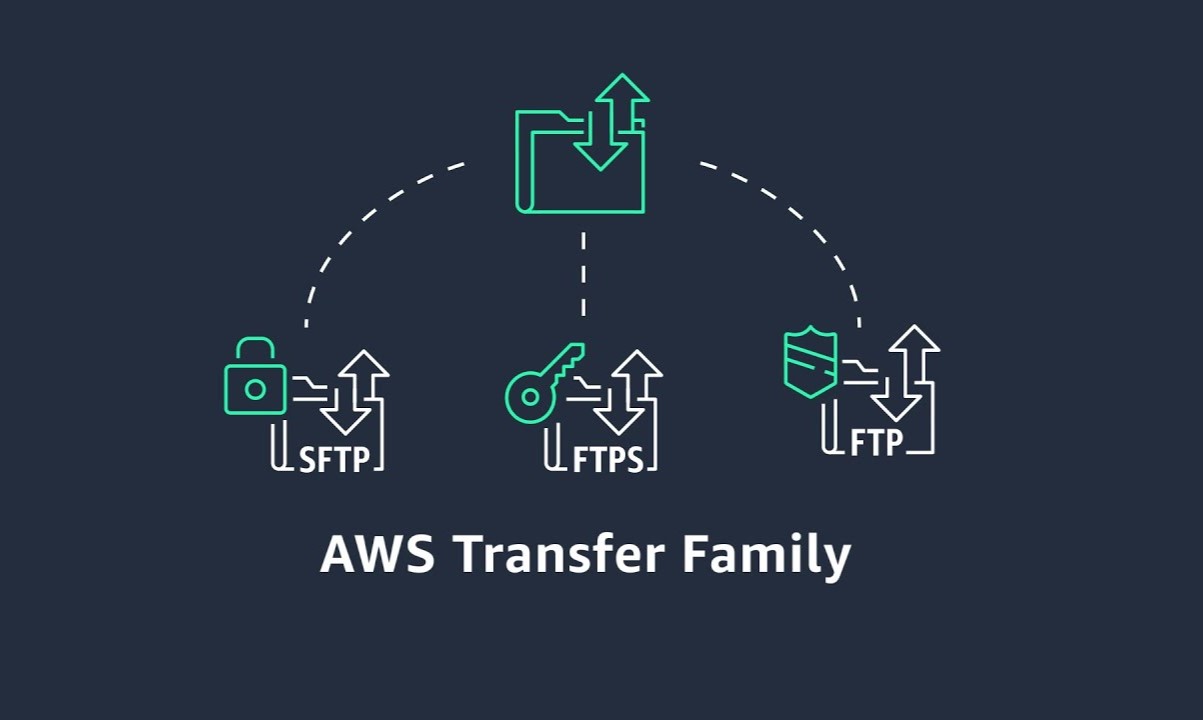
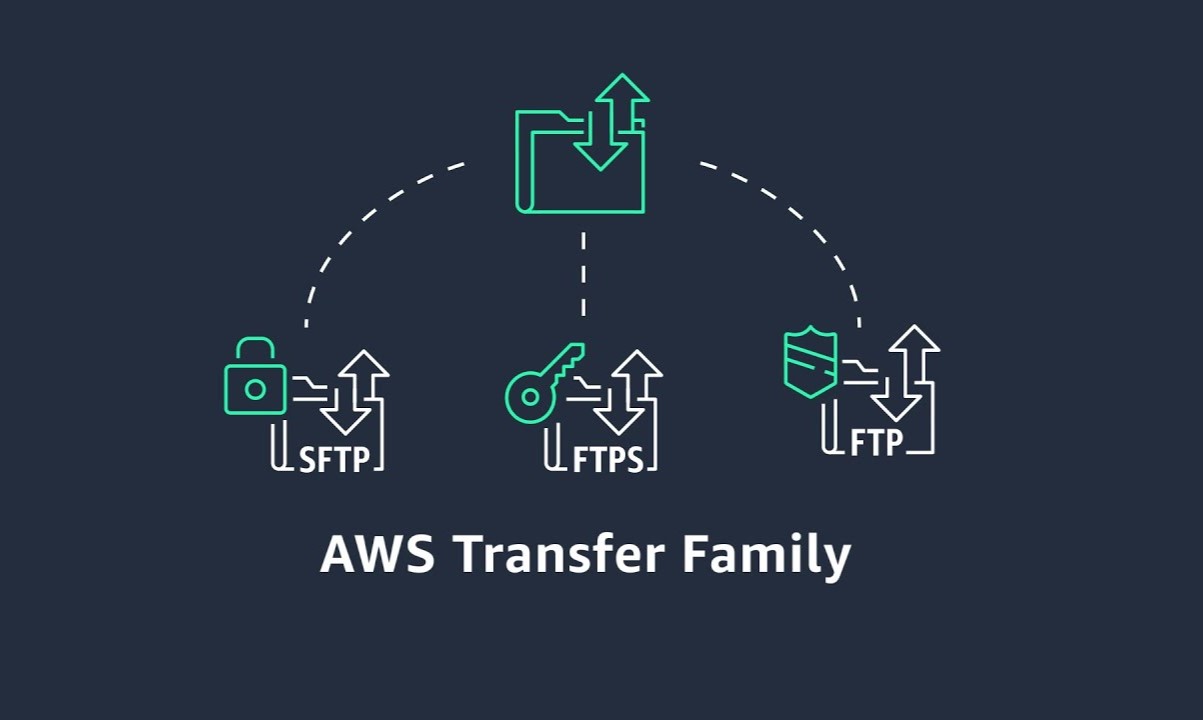
AWS Transfer for SFTP (Secure File Transfer Protocol) is a fully managed service that enables the transfer of files into and out of Amazon S3 storage. It provides a secure and scalable solution for businesses and individuals to transfer files over the internet using the SFTP protocol. With AWS Transfer for SFTP, users can seamlessly migrate their file transfer workflows to AWS without needing to modify existing applications or manage any SFTP servers.
AWS Transfer for FTPS (File Transfer Protocol Secure) is an extension of the AWS Transfer service that supports FTPS, a secure version of the traditional FTP protocol. This service allows users to transfer files using FTPS into and out of Amazon S3, providing a secure and reliable method for file transfer operations.
Both AWS Transfer for SFTP and FTPS offer a fully managed infrastructure, eliminating the need for users to provision or manage any servers. This allows businesses to focus on their core operations without the overhead of maintaining file transfer infrastructure. Additionally, AWS Transfer for SFTP and FTPS integrates seamlessly with other AWS services, enabling users to leverage the full capabilities of the AWS ecosystem for their file transfer needs.
By leveraging AWS Transfer for SFTP and FTPS, organizations can benefit from enhanced security, scalability, and reliability for their file transfer operations. The service provides encryption at rest and in transit, ensuring that data remains secure throughout the transfer process. Furthermore, AWS Transfer for SFTP and FTPS is designed to handle high-throughput file transfer workloads, making it suitable for a wide range of use cases, from small businesses to large enterprises.
In summary, AWS Transfer for SFTP and FTPS offers a robust and fully managed solution for secure file transfers, empowering organizations to streamline their file transfer workflows and leverage the scalability and security of the AWS cloud platform.
Understanding FTP and FTPS
FTP, which stands for File Transfer Protocol, is a standard network protocol used for the transfer of files between a client and a server on a computer network. It has been a fundamental tool for file transfer since the early days of the internet. FTP operates on two separate channels: the command channel, which is used for controlling the conversation between the client and the server, and the data channel, which is responsible for transmitting the actual files.
While FTP is widely used for its simplicity and ease of implementation, it has certain limitations, particularly in terms of security. As FTP transfers data in plain text, it is vulnerable to eavesdropping, data tampering, and other security threats. This inherent lack of security has led to the development of secure alternatives, one of which is FTPS.
FTPS, or File Transfer Protocol Secure, is an extension of FTP that adds support for the Transport Layer Security (TLS) and Secure Sockets Layer (SSL) cryptographic protocols. By incorporating TLS/SSL, FTPS addresses the security concerns associated with traditional FTP. It encrypts the control and data channels, providing a secure and private means of file transfer over a network.
FTPS supports two different modes: implicit and explicit. In implicit mode, the client is required to establish a secure connection with the server before any FTP commands are exchanged. On the other hand, in explicit mode, the client negotiates the security settings with the server before initiating file transfer operations. This flexibility allows users to choose the mode that best suits their security requirements and network configurations.
Understanding the differences between FTP and FTPS is crucial for organizations seeking to secure their file transfer operations. While FTP remains a popular choice for its simplicity, FTPS offers an enhanced level of security by leveraging encryption technologies. By adopting FTPS, businesses can mitigate the risks associated with unsecured file transfers and ensure the confidentiality and integrity of their data during transit.
In summary, FTP and FTPS are both widely used protocols for file transfer, with FTPS offering enhanced security features through the implementation of TLS/SSL encryption. As organizations strive to safeguard their data and comply with regulatory requirements, understanding the nuances of FTP and FTPS becomes essential for making informed decisions about file transfer protocols.
Benefits of FTP and FTPS support for AWS Transfer
-
Enhanced Security: By integrating FTP and FTPS support into AWS Transfer, users can benefit from enhanced security features, including encryption of data in transit and at rest. This ensures that sensitive information remains protected throughout the file transfer process, mitigating the risk of unauthorized access and data breaches.
-
Regulatory Compliance: Many industries and organizations are subject to strict regulatory requirements regarding data security and privacy. The inclusion of FTP and FTPS support in AWS Transfer enables businesses to adhere to compliance standards by implementing secure file transfer protocols that meet regulatory mandates.
-
Seamless Integration: AWS Transfer provides seamless integration with other AWS services, allowing users to leverage the full capabilities of the AWS ecosystem for their file transfer needs. By incorporating FTP and FTPS support, organizations can streamline their file transfer workflows while benefiting from the scalability and reliability of AWS infrastructure.
-
Flexibility and Choice: The availability of both FTP and FTPS support in AWS Transfer offers users the flexibility to choose the file transfer protocol that best aligns with their security and operational requirements. Whether opting for the simplicity of FTP or the enhanced security of FTPS, users can tailor their file transfer operations to suit their specific use cases.
-
Scalability and Performance: AWS Transfer for FTP and FTPS is designed to handle high-throughput file transfer workloads, making it suitable for a wide range of use cases, from small businesses to large enterprises. The service’s scalability and performance capabilities ensure that users can efficiently transfer files of varying sizes and volumes without compromising speed or reliability.
-
Simplified Management: By leveraging AWS Transfer for FTP and FTPS, organizations can offload the management and maintenance of file transfer infrastructure to AWS, allowing them to focus on their core business operations. This eliminates the need for users to provision or manage servers, reducing operational overhead and complexity.
-
Cost-Effective Solution: AWS Transfer for FTP and FTPS offers a cost-effective solution for secure file transfer, as users only pay for the resources they consume. This pay-as-you-go model enables businesses to optimize their file transfer costs while benefiting from the security and reliability of AWS Transfer.
In summary, the inclusion of FTP and FTPS support in AWS Transfer brings a host of benefits to users, ranging from enhanced security and regulatory compliance to seamless integration with AWS services and cost-effective file transfer solutions. By leveraging these capabilities, organizations can elevate their file transfer workflows while maintaining the highest standards of security and reliability.
Setting up FTP and FTPS support for AWS Transfer
Setting up FTP and FTPS support for AWS Transfer is a straightforward process that empowers users to securely transfer files into and out of Amazon S3 storage. The following steps outline the process of configuring FTP and FTPS support within the AWS Transfer service:
-
Accessing the AWS Management Console: Begin by logging into the AWS Management Console and navigating to the AWS Transfer for SFTP and FTPS service.
-
Creating a Server: Within the AWS Transfer service, create a new server instance by specifying the server identity, authentication method, and endpoint configuration. This step involves defining the server’s identity, such as its domain name, and selecting the authentication method, which can include password-based authentication or public key authentication.
-
Configuring Endpoint and Protocol Settings: Configure the server’s endpoint settings, including the protocol selection for FTP or FTPS. Users can choose to enable FTPS by selecting the appropriate protocol and specifying the required security settings, such as the SSL certificate for securing the file transfer operations.
-
Defining User Access: After setting up the server, define user access by creating user accounts with specific permissions for accessing the server and performing file transfer operations. Users can be granted access to specific directories within Amazon S3, ensuring granular control over file access and management.
-
Integrating with Amazon S3: Once the server and user access are configured, integrate the AWS Transfer service with Amazon S3 by specifying the S3 bucket and directory mappings. This step establishes the link between the server and the designated S3 storage, enabling seamless file transfer operations between the server and S3.
-
Testing and Validation: After completing the setup process, perform thorough testing and validation to ensure that the FTP and FTPS support for AWS Transfer is functioning as intended. This involves conducting file transfer operations, verifying user access permissions, and validating the secure transmission of files using the configured protocols.
By following these steps, users can effectively set up FTP and FTPS support for AWS Transfer, enabling secure and efficient file transfer operations within the AWS ecosystem. The seamless integration with Amazon S3, coupled with the robust security features of FTP and FTPS, empowers organizations to streamline their file transfer workflows while maintaining the highest standards of data security and compliance.
Best practices for using FTP and FTPS with AWS Transfer
-
Implement Strong Authentication Mechanisms: Utilize robust authentication methods such as public key authentication or multi-factor authentication to ensure secure access to the FTP and FTPS servers within AWS Transfer. Strong authentication mechanisms help prevent unauthorized access and enhance the overall security posture of file transfer operations.
-
Enforce Encryption Standards: Adhere to industry-standard encryption protocols, such as TLS for FTPS, to encrypt data both in transit and at rest. By enforcing encryption standards, organizations can safeguard sensitive information from unauthorized interception and maintain the confidentiality of transferred files.
-
Regular Security Audits and Monitoring: Conduct regular security audits and implement continuous monitoring of FTP and FTPS servers to detect and mitigate potential security threats. Monitoring tools and security audits help identify anomalies, unauthorized access attempts, and potential vulnerabilities, allowing for proactive security measures.
-
Implement Access Controls and Permissions: Define granular access controls and permissions for users accessing the FTP and FTPS servers, ensuring that individuals have the appropriate level of access based on their roles and responsibilities. This practice minimizes the risk of unauthorized data access and manipulation.
-
Enable Logging and Auditing: Enable comprehensive logging and auditing capabilities to track file transfer activities, user interactions, and system events. Logging and auditing provide valuable insights into file transfer operations, aiding in compliance adherence, troubleshooting, and security incident investigations.
-
Regular Software Updates and Patch Management: Stay current with software updates and security patches for the FTP and FTPS servers to address known vulnerabilities and maintain the integrity of the file transfer infrastructure. Timely updates help mitigate potential security risks associated with outdated software versions.
-
Network Segmentation and Isolation: Implement network segmentation and isolation to restrict access to the FTP and FTPS servers, minimizing the exposure of sensitive data to unauthorized network segments. This practice enhances the overall security posture of the file transfer environment.
-
Disaster Recovery and Backup Strategies: Establish robust disaster recovery and backup strategies to ensure the availability and integrity of transferred files in the event of unforeseen incidents. Regular backups and disaster recovery planning mitigate the risk of data loss and support business continuity.
-
Compliance with Regulatory Standards: Adhere to industry-specific regulatory standards and compliance requirements governing data security and privacy. Aligning FTP and FTPS file transfer practices with regulatory standards ensures that organizations meet legal obligations and industry guidelines.
-
Employee Training and Awareness: Provide comprehensive training and awareness programs for employees involved in file transfer operations, emphasizing best practices, security protocols, and data handling procedures. Educated personnel contribute to a secure file transfer environment.
By incorporating these best practices, organizations can optimize the use of FTP and FTPS with AWS Transfer, ensuring secure, compliant, and efficient file transfer operations within the AWS ecosystem.